G Network Configuration for Advanced Threat Protection
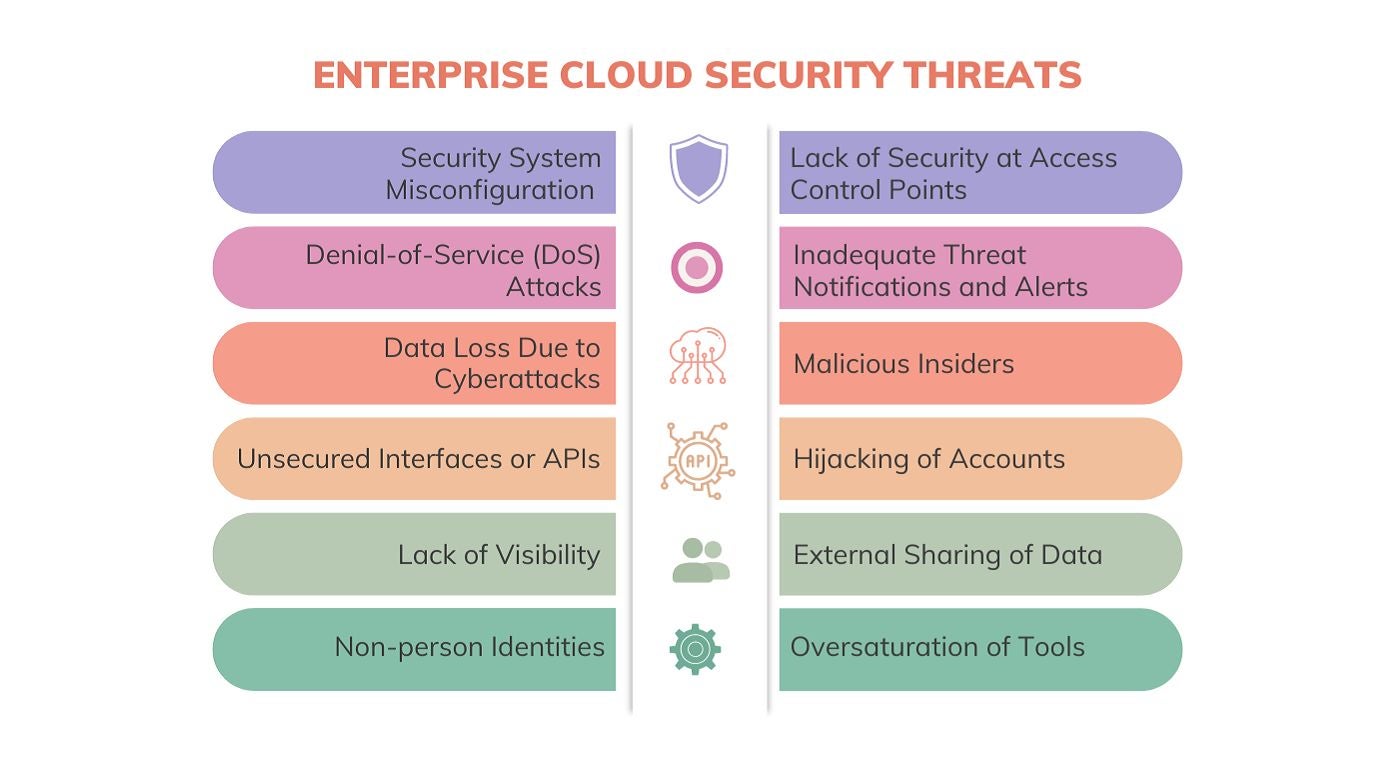
In today's digital landscape, advanced threats are becoming increasingly sophisticated, making it challenging for organizations to protect their networks from cyber-attacks. A well-configured network is crucial to prevent such threats, and G Network Configuration for Advanced Threat Protection is a crucial aspect of network security.
What is G Network Configuration for Advanced Threat Protection?
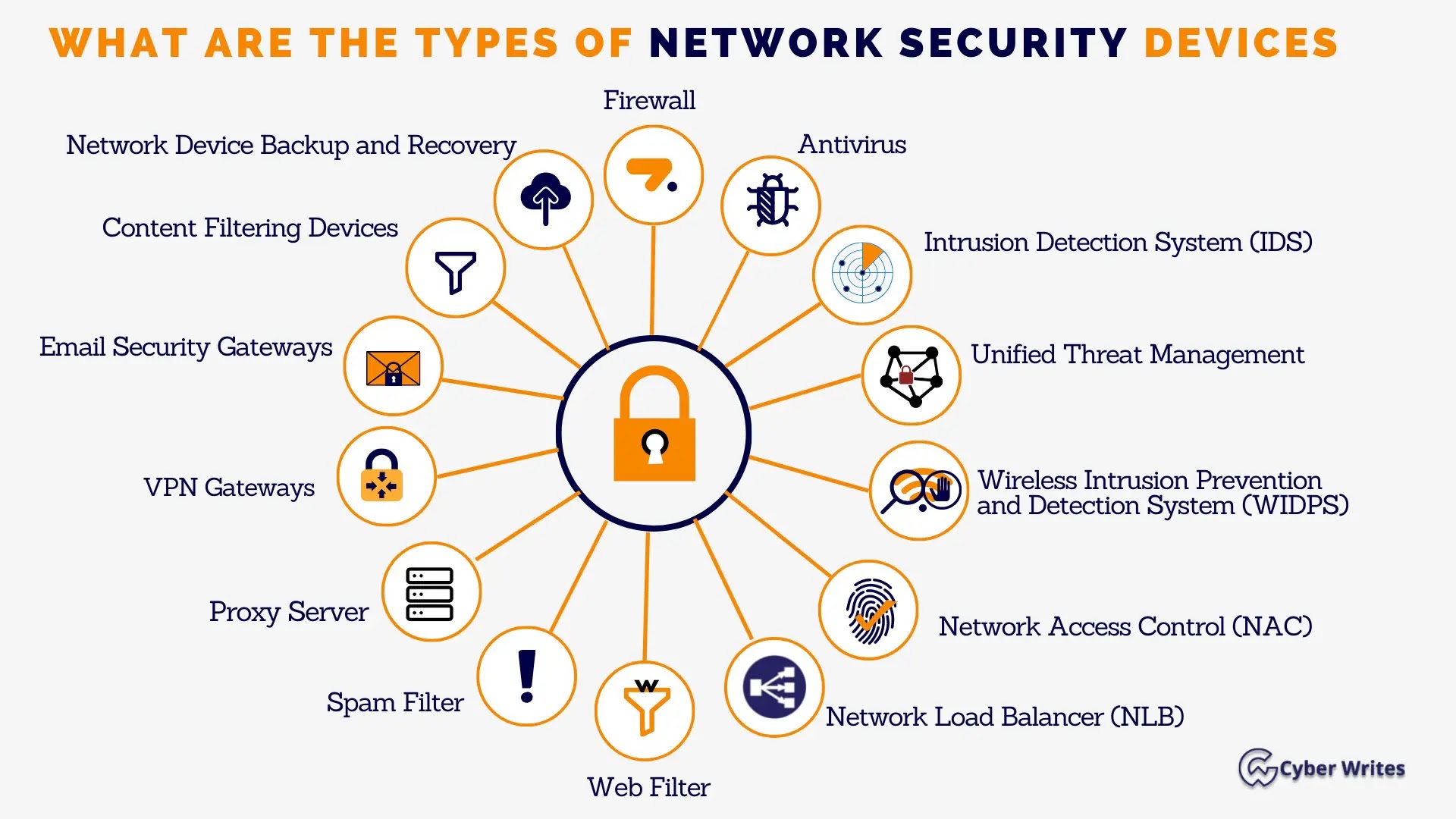
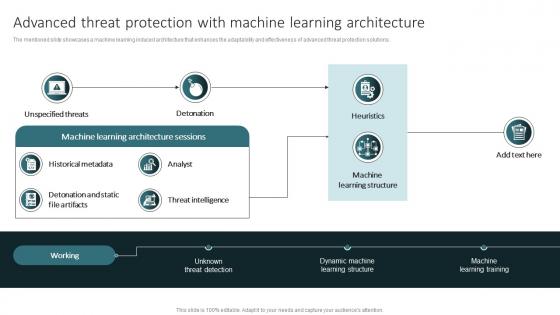
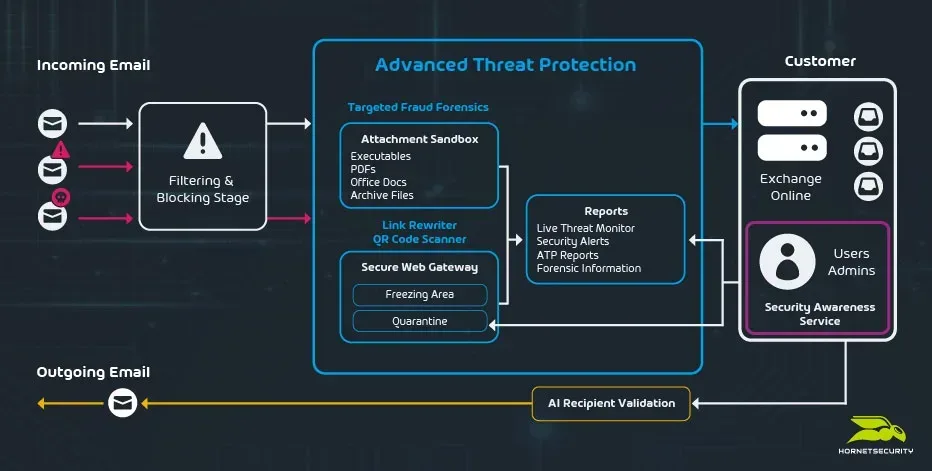
G Network Configuration for Advanced Threat Protection is a security solution that helps protect your organization's network from advanced threats by blocking malicious traffic at the network level. This solution is designed to detect and prevent sophisticated cyber-attacks, including phishing, exploits, and malware.
Benefits of G Network Configuration for Advanced Threat Protection
- Improved Network Security: G Network Configuration for Advanced Threat Protection helps prevent advanced threats from entering your network, improving overall network security and reducing the risk of data breaches.
- Compliance with Regulatory Requirements: Organizations in regulated industries, such as finance and healthcare, must maintain stringent network security to comply with regulatory requirements.
- Enhanced Visibility and Control: This solution provides detailed visibility into network traffic, allowing administrators to identify and block malicious activity in real-time.
This particular example perfectly highlights why G Network Configuration For Advanced Threat Protection is so captivating.
G Network Configuration Best Practices
To get the most out of G Network Configuration for Advanced Threat Protection, follow these best practices:
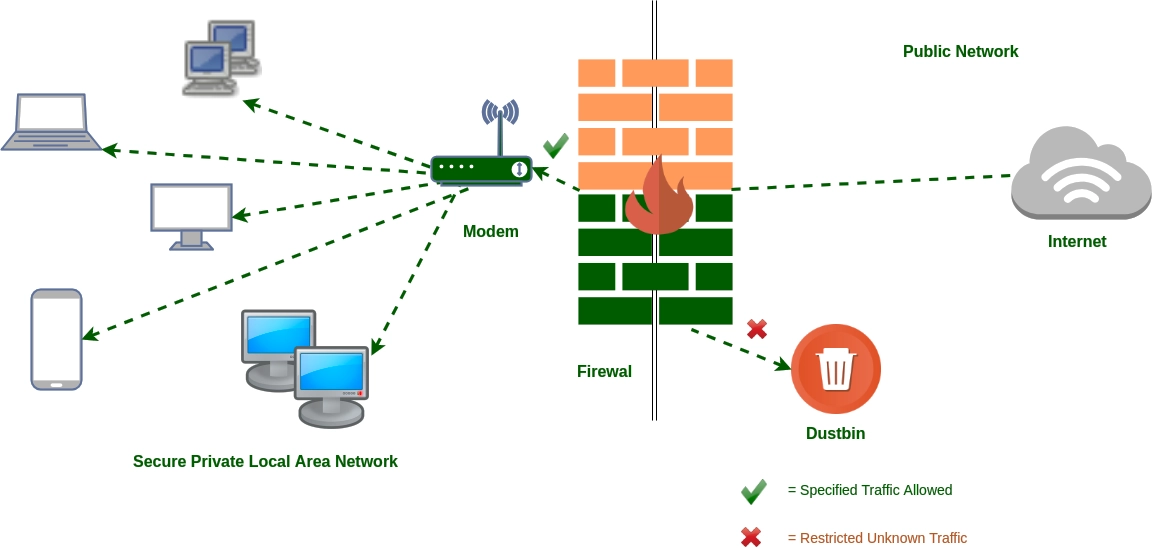
- Implement a Robust Firewall Policy: A well-configured firewall policy is crucial to blocking malicious traffic and preventing advanced threats from entering your network.
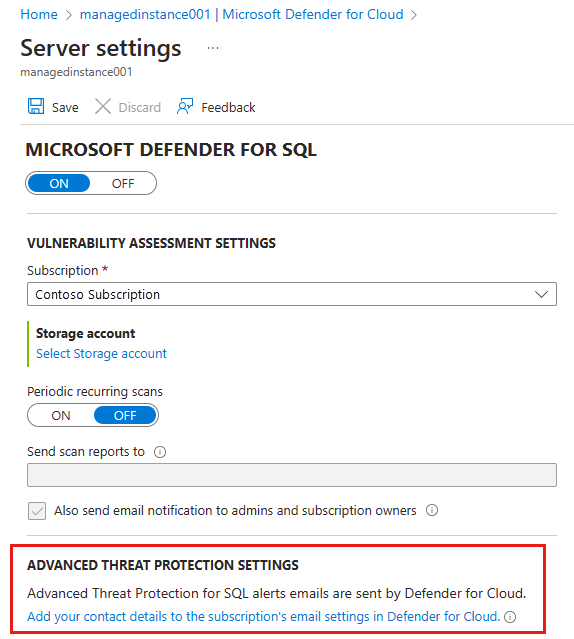
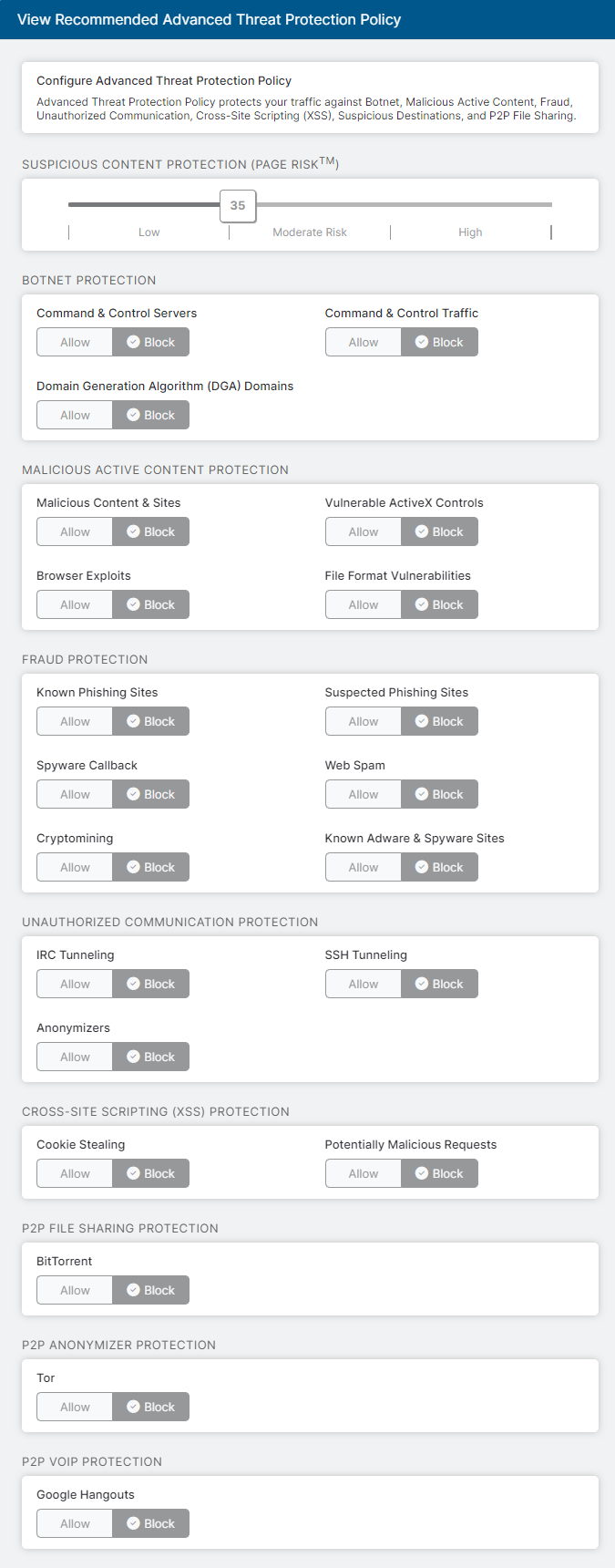
- Configure Advanced Threat Protection Settings: Adjust Advanced Threat Protection settings to suit your organization's needs, ensuring that you are protecting your network from the most relevant threats.
- Regularly Monitor and Update Your G Network Configuration: Regularly review and update your G Network Configuration to ensure that you have the most up-to-date protection against emerging threats.
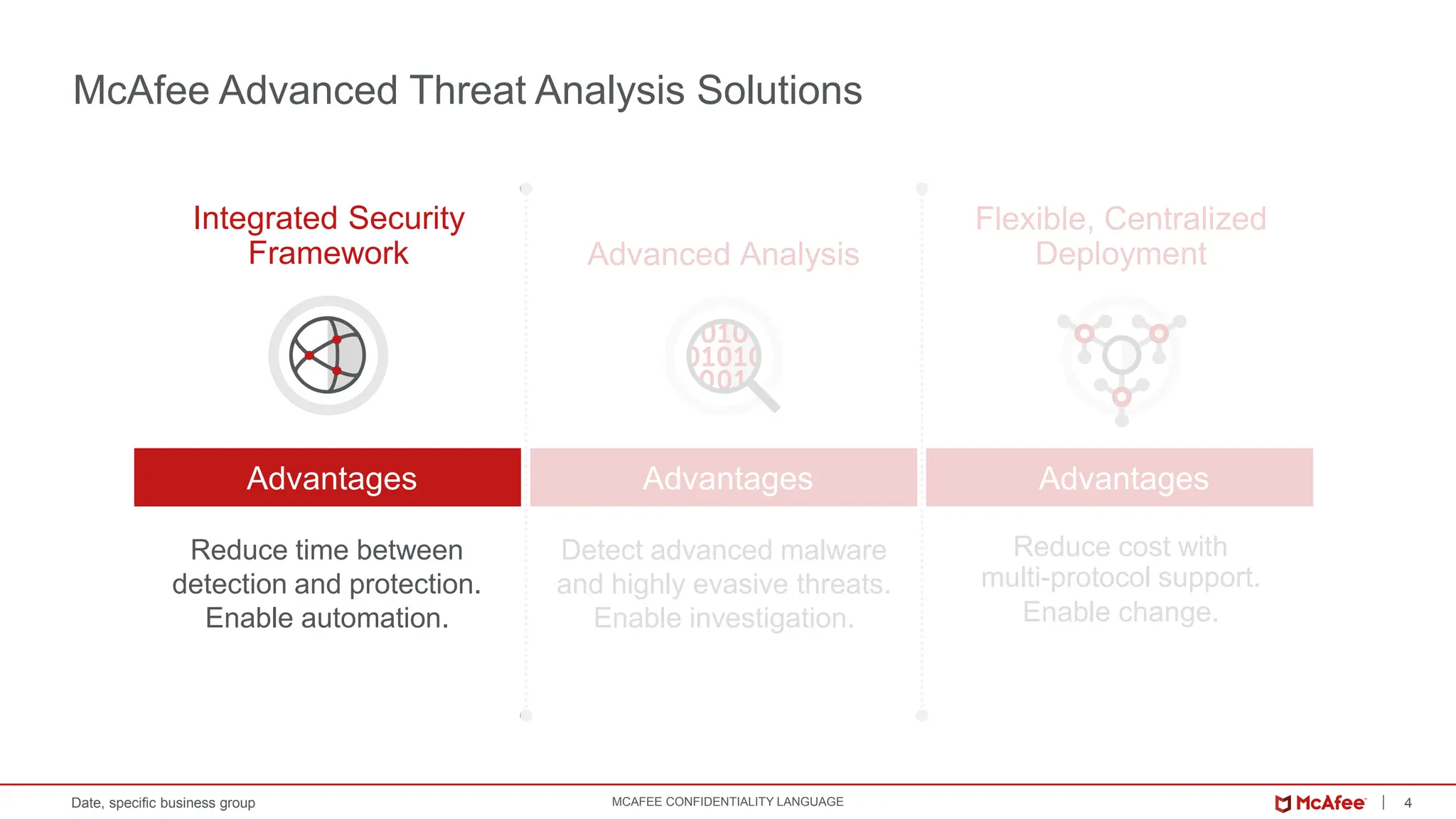
Advanced Threat Protection is particularly important for organizations with high-security needs, such as:
- High-Security Departments: Apply strict network protection policies to departments with higher security needs, like R&D or finance.
- Compliance and Regulatory Requirements: In certain industries, maintaining stringent network security is part of regulatory compliance.

This particular example perfectly highlights why G Network Configuration For Advanced Threat Protection is so captivating.
Real-World Examples of G Network Configuration for Advanced Threat Protection
Here are some real-world examples of G Network Configuration for Advanced Threat Protection:
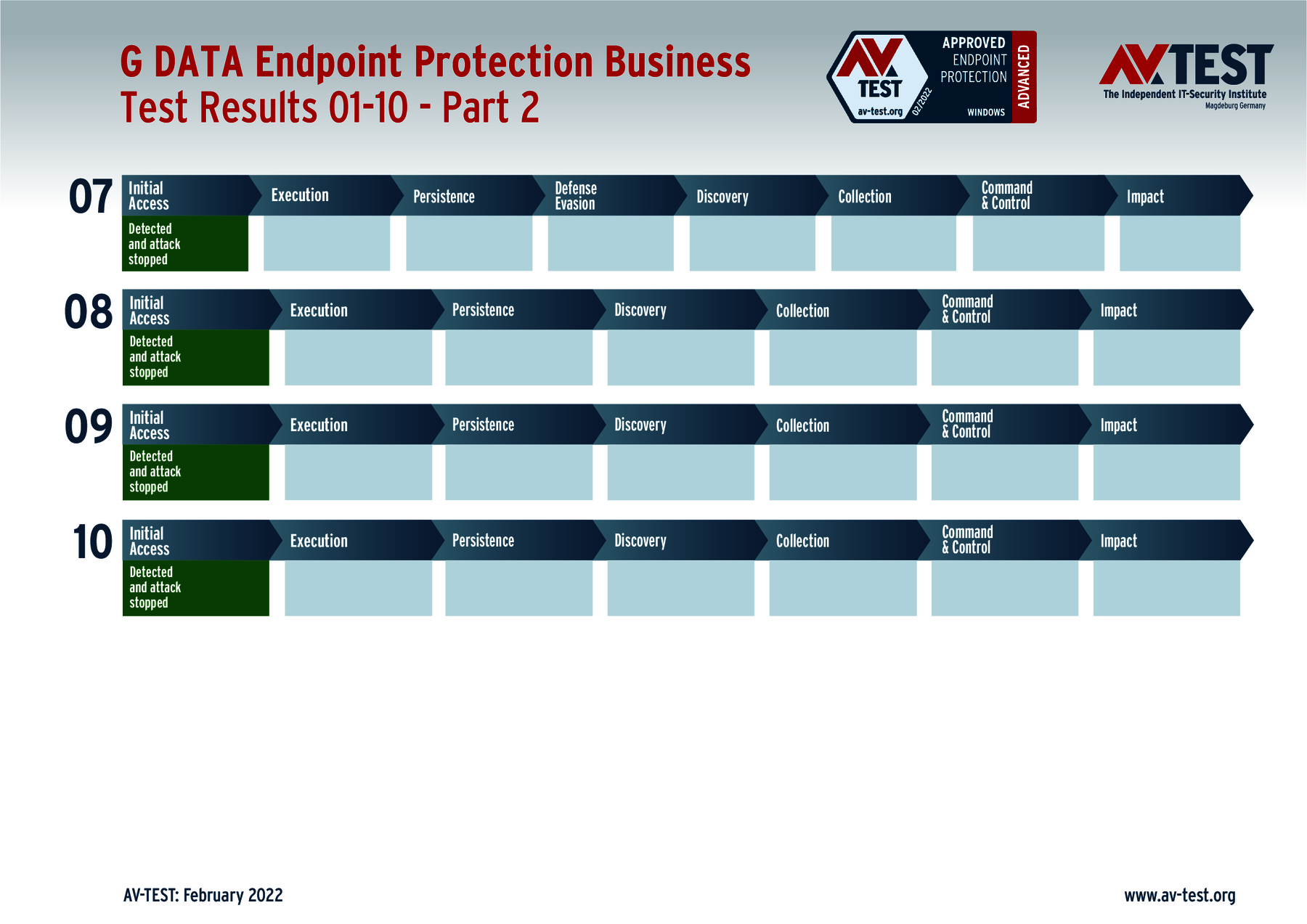
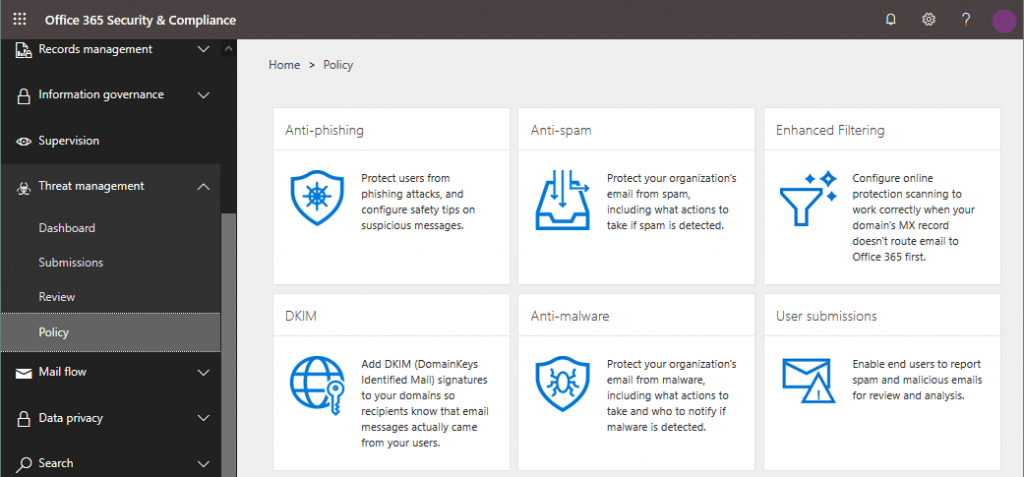
- Microsoft Defender ATP: Windows Defender ATP (Advanced Threat Protection) helps protect your organization's endpoint devices from advanced threats.
- Cisco Firepower NGFW: Cisco Firepower Next-Generation Firewall (NGFW) includes Advanced Threat Prevention, which defends your network against both commodity threats and advanced threats.
- Palo Alto Networks: Palo Alto Networks' next-generation firewall threat intrusion prevention subscriptions protect and defend your network from commodity threats and advanced persistent threats (APTs).
Conclusion
G Network Configuration for Advanced Threat Protection is a critical component of network security that helps protect your organization from advanced threats. By following best practices and adjusting settings to suit your organization's needs, you can ensure that your network remains secure and protected against emerging threats.